
Deploying Prophaze WAF On-Premises On AWS
Protect Your on-premises AWS Workloads with Prophaze WAF Deploying Prophaze WAF on your on-premises AWS workloads allows you to have

Protect Your on-premises AWS Workloads with Prophaze WAF Deploying Prophaze WAF on your on-premises AWS workloads allows you to have

Overview On-premises means that a business installs and controls its own software, hardware, or infrastructure within its physical space. Prophaze
Prophaze’s WAF-as-a-Service Elevate Your Web Application Security with Prophaze’s WAF Prophaze’s WAF-as-a-Service is a reliable and effective solution to secure

What is SQL Injection? SQL injection is a type of cyber attack that targets web applications that use Structured Query
Prophaze offers a wide range of cybersecurity solutions, including securing third-party API integrations. Helps to identify and mitigate potential security
Advantages of Prophaze WAF As A Service Customer Retention with WAF as a Service WAF configuration is tricky and with

Web Application Firewalls (WAF) have existed for quite some time to safeguard web applications by inspecting HTTP traffic. Traditionally, on-premises WAFs
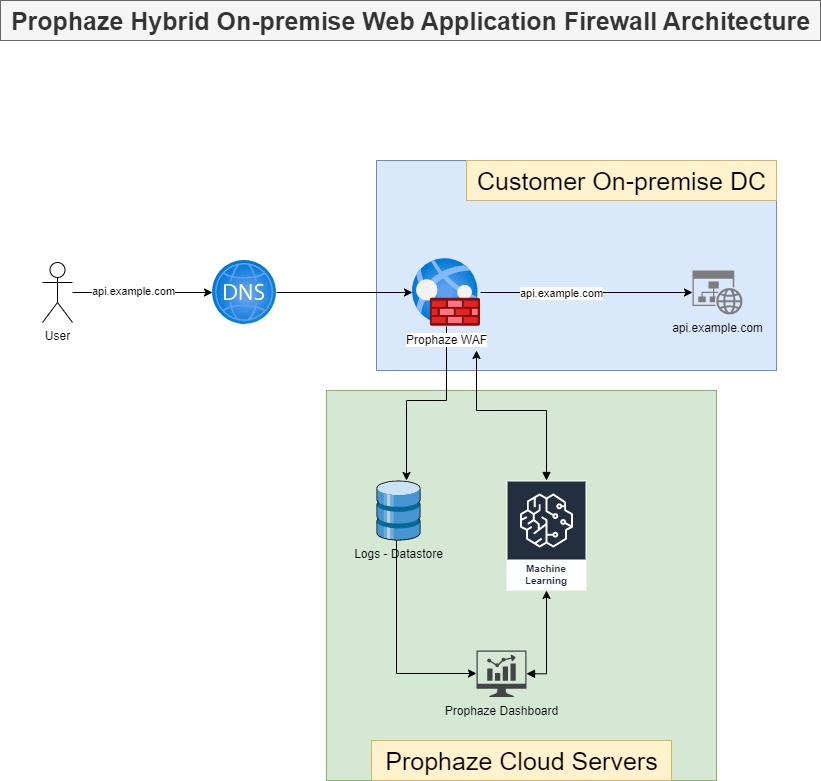
On-Premises WAF Prophaze WAF Supports On-Premises Prophaze WAF support on-premises deployment to ensure compliance with security in industries such as
Security For Examination Portals The education sector has also been impacted greatly by the digitalisation post-Covid pandemic. Services have been
Prophaze WAF 3.0 Secure, Simpler, and Safer Prophaze WAF 3.0 is a Distributed proactive web security platform designed to defend

Leading Power Industry strengthens API Security with Prophaze The reason behind choosing Prophaze is to reduce internal complexity, enhance API

Prophaze Helps the Healthcare Industry from ransomware attacks Such a company facing this kind of attacks deployed Prophaze, and it

What is Session Hijacking? Session Hijacking is the type of attack in which the attacker takes over or hijacks a
Description Check Point ZoneAlarm Extreme Security before 15.8.211.19229 allows local users to escalate privileges. This occurs because of weak permissions

What is DNS and how does it work? DNS is the abbreviation for Domain Name System. The task of the

What is Content Security Policy (CSP)? Content Security Policy (CSP) is an additional layer of security on the HTTP browser

What is Swagger? Swagger is the way of defining the structure of APIs (Application Programming Interface). Swagger is specifically developed

What is a Supply Chain Attack? The supply chain includes everything from the delivery of materials from suppliers to manufacturers
What Is Clickjacking? Users are tricked into believing they are clicking on one thing when they are actually clicking on
What Is Remote Code Execution? Remote Code Execution or RCE, also known as arbitrary code execution is a network vulnerability

What is IoT Security? IoT (Internet of Things) is a recent technology at least in the domestic sector. It comprises

What is 2FA? 2FA stands for Two Factor Authentication and has become a near requirement for securing user accounts on

What is a Cloud Access Security Brokers (CASB)? CASB is the acronym for Cloud Access Security Brokers. A CASB is
Zero-Configuration Web Application and API Protection for Kubernetes Zero-Configuration Web Application and API Protection (WAAP), DDoS protection and Bot Mitigation