Blogs
- Latest Blog
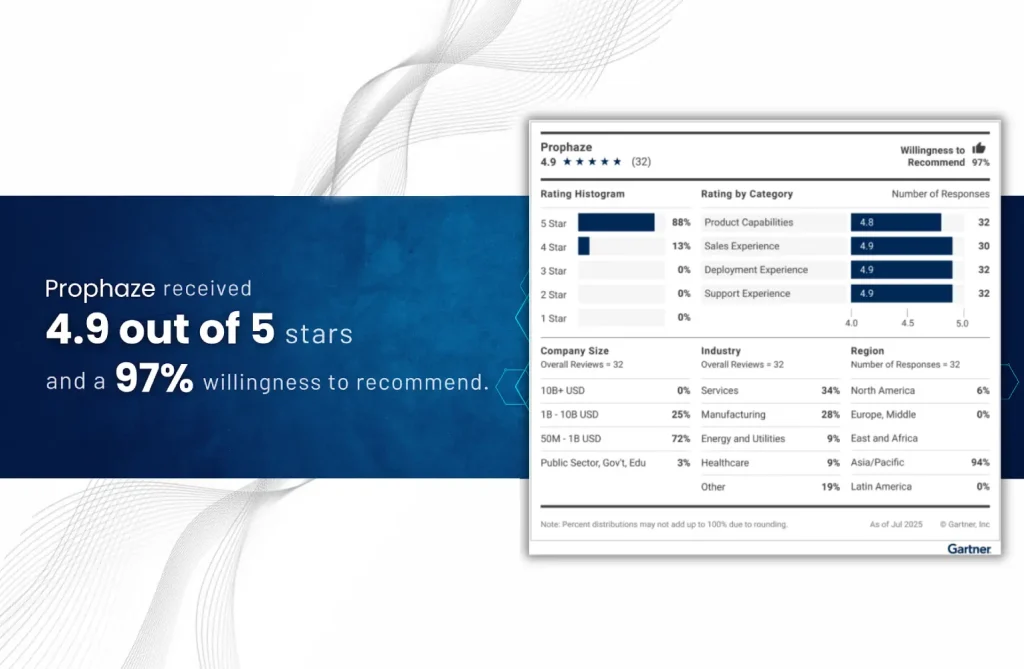
“Voice of the Customer” 2025 for Cloud Web Application and API Protection
- Blog
For more than a decade, Red Hat has helped organizations accelerate cloud-native transformation with Kubernetes
- Blog
The IT and SaaS sectors are the primary targets of the “identity-centric” and “API-first” attack
- Blog
Choosing a Web Application and API Protection (WAAP) platform is no longer simply a feature
- Blog
The System Running Your Factory Is Under Active Attack In SAP ERP security 2026, manufacturing
- Blog
The Gartner WAAP Signal Every Security Buyers Needs to See When enterprises evaluate modern application
- Blog
WAAP in Manufacturing No Longer Optional Manufacturing environments are no longer isolated operational systems. Modern
- Blog
Why API Security Has Become the Biggest Blind Spot Across All Businesses APIs are the
- Blog
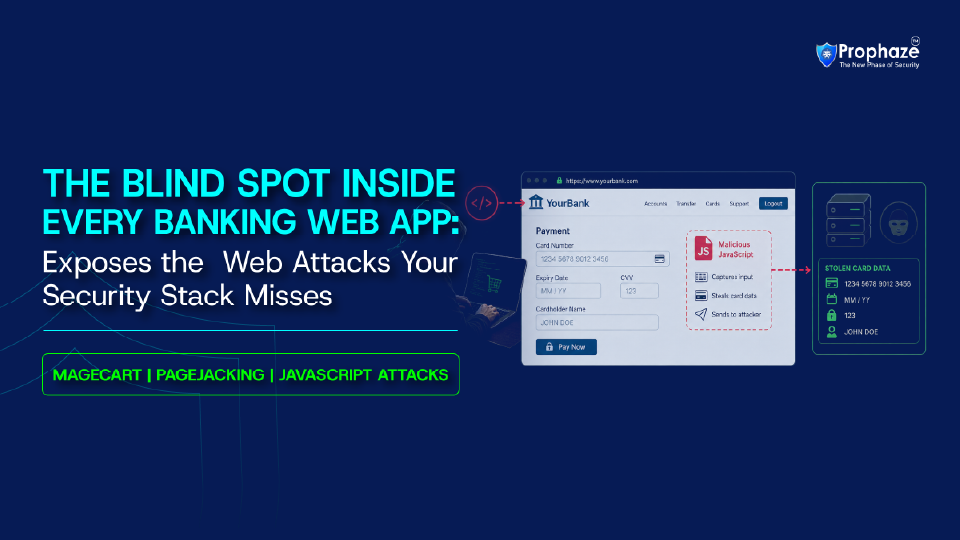
Stop Magecart Attack In Banking Applications Before They Expose Customer Data Magecart attacks on banking
- Blog
Application and API Security for BFSI: Why Traditional Defenses Are Failing Application and API security
- Blog
The Attack Nobody Is Logging: Server-Side Request Forgery in Healthcare Behind your perimeter firewalls, deep
- Blog
The Pen-and-Paper Reality: The Urgent Need for Web Application and API Security in Healthcare Web
- Blog
Exposing Partial Inspection Evasion in Modern WAFs In 2026, organizations widely deploy Web Application Firewalls