Enterprise WAAP. Managed Your Way.
- Self-Serve or Fully Managed
- Full-Stack Protection.
- No Add-Ons.
- Predictable Cost.
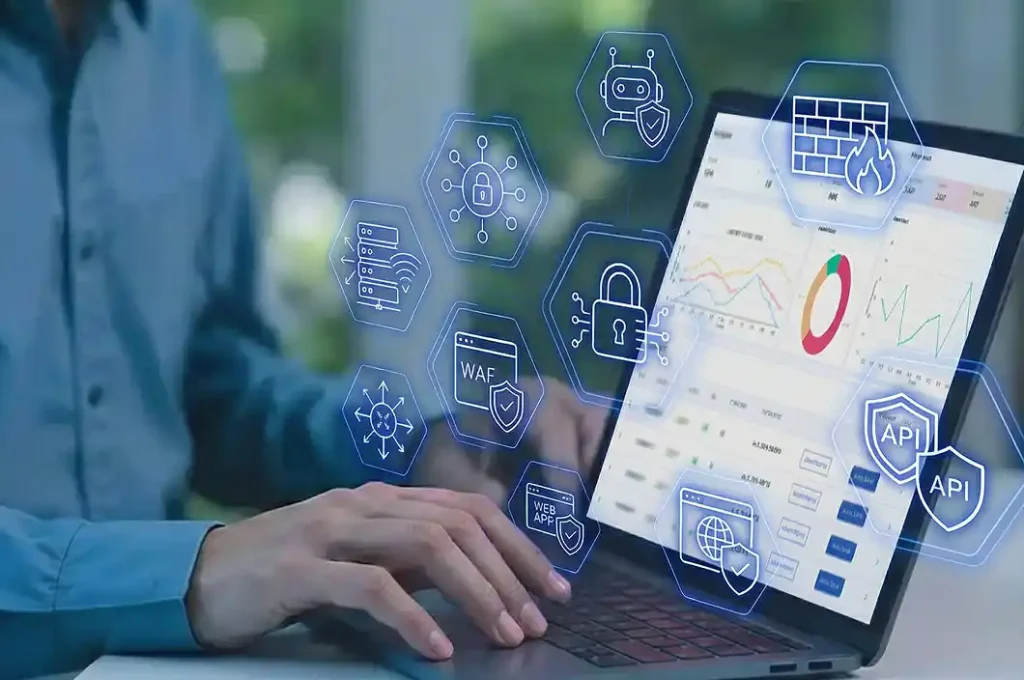
AI-powered and backed by 24×7 threat analysts, Prophaze WAAP stops DDoS attacks, malicious bots, API threats, OWASP Top 10 risks, and zero-day exploits before they reach your applications.
- Unified Web, API, Bot & DDoS Protection
- Kubernetes-native WAAP
- AI/ML - Anomaly Detection
- Inline, Hybrid & Multi-Cloud
- Deploy in 15 minutes























Even the best WAFs are still just tools. They work well, Until they don’t.
Not with Prophaze.
- Who responds when I’m under attack?
- Am I getting complete protection, or a base product with paid add-ons?
- Is security truly managed, or still my problem?


Meet Prophaze: The Fully Managed, Fully Featured Web Application & API Security You Can Trust.
Core Value Statement
Core Differentiator
Fully Featured by Default

Powered by AI and Backed by Human Experts

Flexible. Infrastructure Agnostic.

Fully Managed from End to End

Intelligent Protection in Four Layers
Traffic Analysis
AI inspects every HTTP/S request in real-time, analyzing headers, payloads, and behavioral patterns against learned baselines.
Threat Detection
ML algorithms identify SQL injection, XSS, DDoS, bot traffic, API abuse, and zero-day exploits using multi-vector analysis.
Intelligent Response
Automated actions include blocking, rate limiting, virtual patching based on threat severity.
Human in the Loop
Security experts validate critical threat responses, fine-tune detection logic, and ensure contextual accuracy across complex or evolving attack scenarios.
Continuous Learning
System automatically adapts to new attack patterns and application changes without manual rule updates.
Deploy Anywhere, Protect Everything

Cloud-Native (AWS, Azure, GCP)
On-Premises

Hybrid Cloud
Kubernetes / Container-based
Multi-Cloud deployments

Supported Platforms
AWS EC2, Azure VMs, GCP Compute, Kubernetes, Docker, On-Prem Hardware & Private Cloud
Deployment Time
15 minutes average with automated configuration
Integration Methods
Reverse Proxy, DNS-based, API Gateway, Service Mesh
Performance Impact
<5ms latency added, supports 10,000+ requests/sec on a single on‑prem instance
Scalability
Auto-scaling based on traffic, supports unlimited applications
High Availability
Active-active clustering, 99.99% SLA, automatic failover
Enterprise-Grade Security, Startup-Speed Deployment
For Security Teams
- Automated threat hunting and incident response
- Real-time attack visualization dashboard
- Custom security policies with one click deployment
- Integration with SIEM, SOAR, and monitoring tools
- Compliance reporting for SOC 2, HIPAA, PCI DSS, GDPR

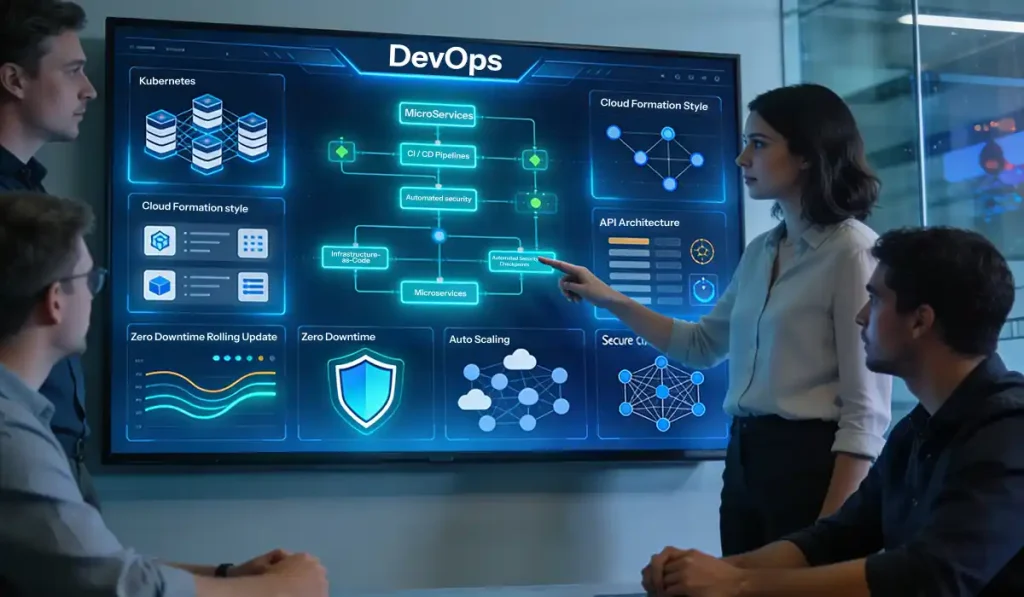
For DevOps Teams
- Deploy via Terraform, Helm charts, or CloudFormation
- Native Kubernetes integration for microservices protection
- CI/CD pipeline integration with automated security testing
- API-first architecture with comprehensive REST API
- Zero downtime updates and automatic scaling
For Business Leaders
- Reduce security costs by 60% vs. traditional WAF solutions
- Eliminate false positives that damage customer experience
- Demonstrate compliance for customer audits and certifications
- 24/7 expert support with <15 minute response time
- Predictable pricing with no hidden fees or traffic limits

Built for Your Industry’s Unique Security Challenges
Why Security Teams Choose Prophaze






Calendar booking with solutions engineer
Easily schedule a dedicated session with our Solutions Engineer to walk you through product capabilities, clarify technical queries, and help tailor the right solution for your needs.
What our clients say about staying Secure with us
Discover how our trusted cybersecurity solutions have empowered businesses to operate with confidence.

How Prophaze Compares to Alternatives
Making a security investment decision requires seeing all the options clearly. That’s why we’ve created this transparent comparison. No marketing fluff, just real differences that impact your security operations and budget.

Substantial extra costs for advanced features such as API security, Bot mitigation, custom rules etc.
Lack of flexibility WAF is bundled either to a global distributed infrastructure or to a physical appliance.

Complete data sovereignty, data will be handled in the country, region, or data center of your choice
Supports all infrastructures, use our cloud or yours, deploy in your private data center, as a reverse proxy, or as a Kubernetes sidecar
Fully managed service, including integration, tuning, 24/7 support, SOC, and threat response, all at just the cost of a WAF
Resources & Learning Center
Learn, Explore, and Master Modern Application Security.
- Buyer’s Guides
- Industry Use Cases
- Product Briefs
- Webinars


Our Resources
- Blog
Every second your store is down, a customer is checking out somewhere else. It’s peak
- Blog
The Healthcare API Attack Surface Is Bigger Than Most Organizations Realize Healthcare has never been
- Blog
ON-DEMAND WEBINAR RECORDING Closing Visibility Gaps in WAAP: Addressing API Discovery, Posture, and Runtime Protection
Choose how You Want to get Started
- Live product walkthrough
- Custom use case review
- Architecture consultation
- 30-minute session




