What is REST API?
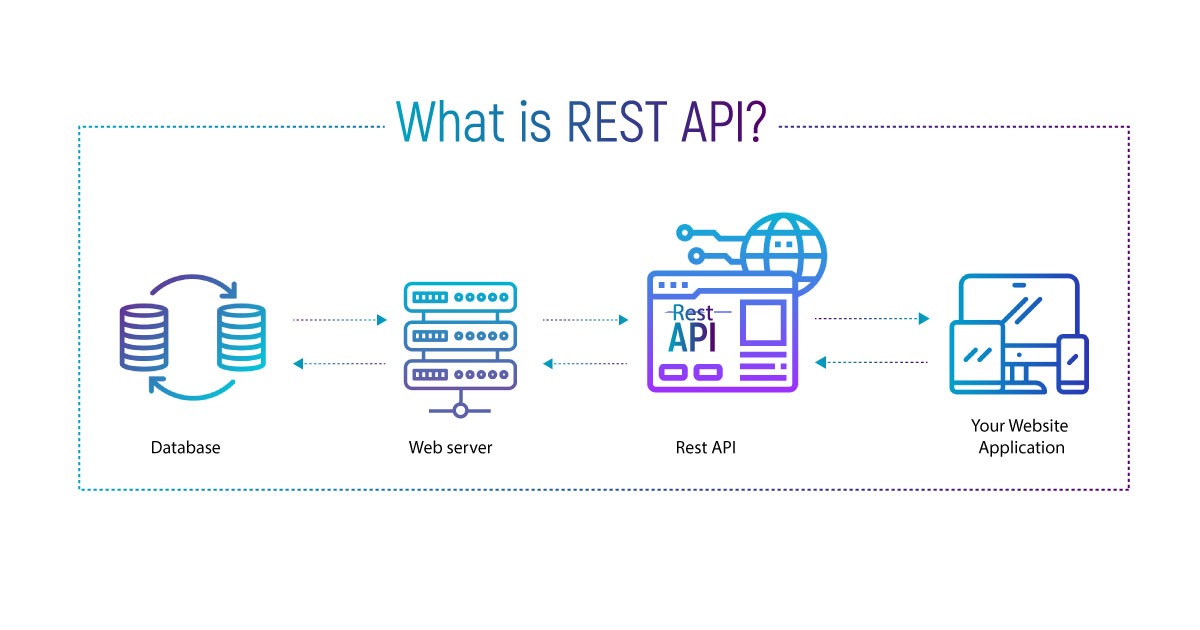
REST is the acronym of Representational State Transfer (REST). It is an architectural style or pattern that has a set of constraints or rules for creating web services. REST API is an Application Programming Interface used for creating REST web services, which should follow the REST architectural style. When a REST API is called, the server will Transfer a Representation of the State (REST) of the requested resource to the client. The representation of the state can be in JSON, XML or HTML formats. For example: When a REST API is called to fetch some user details (the resource), then the API will return the state of that user (Name, Age, DOB, Address etc).
Architectural Constraints of REST API

Uniform Interface
The Uniform Interface means, all the requests should have the same appearance or interface irrespective of the type of browsers, operating systems, devices, different applications or any scripts which are used by the clients. Each request should contain all the information required for the server to process the request and each response should contain all the information that is required for the client to understand the server response.
Stateless
Stateless means, the server should not store any information about the user session. Each request should include all the information needed to complete the request from the client to the server.
Cacheable
Every response from the server should include whether it is cacheable or not-cacheable. If the response is cacheable, it should specify the duration of the data for how long it can be cached at the client side.
Client-Server
The client will be sending the requests to the server and the server processes these requests and send back the response to the client. The client deals with user interactions and the server is storing the data.
Layered System
The architecture of an application may include multiple layers between the client and the server. There can be many servers between the client and the main server, which acts as separate layers like a security layer, a caching layer, a load-balancing layer, or other functionality. Each layer doesn’t know anything about any layer other than that of the immediate layer. These layers should not affect the request and the response from the client and server.
Code on Demand
This constraint is optional. REST allows client to download and execute the code in the form of applets or scripts. When the client requests code, the server will send the code as response and then client can execute that code.
Securing REST API
Below mentioned are different ways to secure REST API.
-
Least Privilege: An entity should be given only the required permissions to perform an authorized action.
-
The default access of a user to any resource should be denied, if they are not authorized for that action.
-
Encryption: Use HTTPS and TLS. Communicating with a TLS certificate protects all access credentials and API data using end-to-end encryption.
-
Use Password Hash : Always use hashed password for password security. Hashing Algorithms like PBKDF2, bcrypt, scrypt etc can be used for password hashing.
-
Use API keys or Tokens for authentication. OAuth 2 is a secure token-based authentication mechanism that can be used in an API for secure user authentication and authorization. Another token-based authentication method is using JSON Web Token (JWT). JWTs are digitally-signed authentication tokens containing JSON-formatted data about the user.
-
Use input validations.