CVE-2022-22486 : IBM TIVOLI WORKLOAD SCHEDULER 9.4/9.5/10.1 XML EXTERNAL ENTITY REFERENCE
Description IBM Tivoli Workload Scheduler 9.4, 9.5, and 10.1 is vulnerable to an XML External Entity Injection (XXE) attack when
Description IBM Tivoli Workload Scheduler 9.4, 9.5, and 10.1 is vulnerable to an XML External Entity Injection (XXE) attack when
Description Sofia-SIP is an open-source SIP User-Agent library, compliant with the IETF RFC3261 specification. In affected versions Sofia-SIP **lacks both
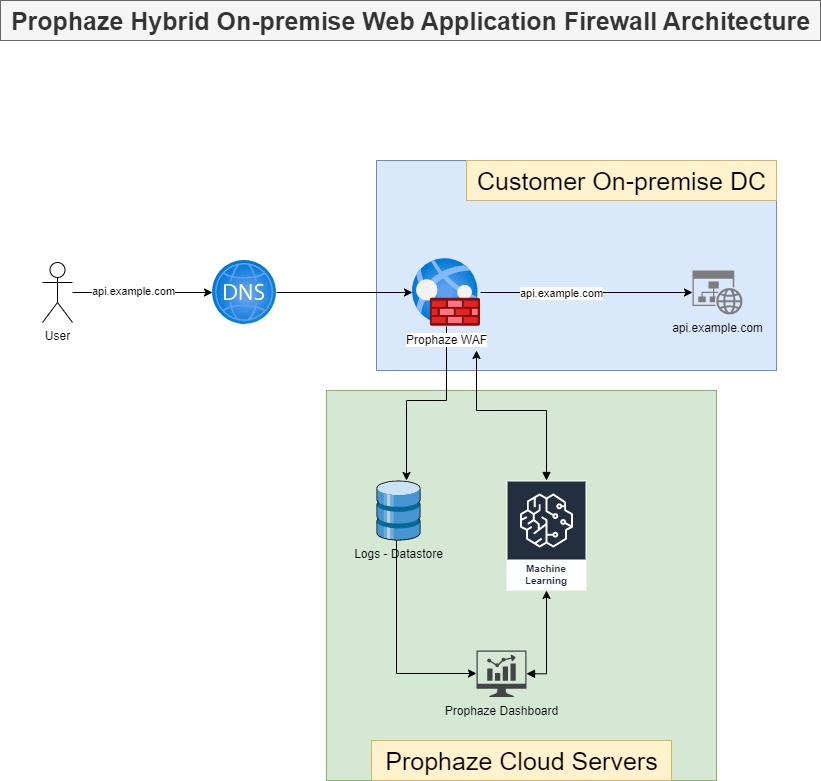
On-Premises WAF Prophaze WAF Supports On-Premises Prophaze WAF support on-premises deployment to ensure compliance with security in industries such as
Description Apache Dubbo is a java based, open source RPC framework. Versions prior to 2.6.10 and 2.7.10 are vulnerable to
Description lxc-user-nic in lxc through 5.0.1 is installed setuid root, and may allow local users to infer whether any file

Description authentik is an open-source Identity Provider focused on flexibility and versatility. Versions prior to 2022.11.4 and 2022.10.4 are vulnerable
Description IBM AIX 7.1, 7.2, 7.3, and VIOS 3.1could allow a non-privileged local user to exploit a vulnerability in CAA
Description xrdp is an open source project which provides a graphical login to remote machines using Microsoft Remote Desktop Protocol
Prophaze WAF 3.0 Secure, Simpler, and Safer Prophaze WAF 3.0 is a Distributed proactive web security platform designed to defend

Prophaze Helps the Healthcare Industry from ransomware attacks Such a company facing this kind of attacks deployed Prophaze, and it

Description A remote code execution (RCE) vulnerability in Optica allows unauthenticated attackers to execute arbitrary code via specially crafted JSON
Why is Container Security Important? A thorough security evaluation must include container security as a crucial component. Using a combination
Description Pimcore is an open source data and experience management platform. Prior to version 10.5.9, the user controlled twig templates
What is PCI DSS? The Payment Card industry data security (PCI DSS), was unfolded to encourage and enhance card holder
Description Due to an issue with incorrect sudo permissions, Zimbra Collaboration Suite (ZCS) suffers from a local privilege escalation issue
What is SSL? SSL stands for Secure Sockets Layer. It is a standard technology for establishing an encrypted link between

What is Directory Traversal? Directory traversal is also known as file path traversal. It is a web security flaw that
What Is Credential Stuffing? A cyberattack known as “credential stuffing” occurs when a cybercriminal gains access to user accounts at

What is REST API? REST is the acronym of Representational State Transfer (REST). It is an architectural style or pattern

What is Session Hijacking? Session Hijacking is the type of attack in which the attacker takes over or hijacks a

What is DNS and how does it work? DNS is the abbreviation for Domain Name System. The task of the

GDPR (General data protection regulation) is regulation to provide uniform data protection by eliminating the inconsistencies in national laws of
Description This Vulnerability in NIS-HAP11AC is caused by an exposed external port for the telnet service. Remote attackers use this

What is Content Security Policy (CSP)? Content Security Policy (CSP) is an additional layer of security on the HTTP browser