APIs Under Attack, Prophaze Secures Every Call
Discover every API, block zero‑day attacks and bots, and enforce policies at scale without slowing your developers down.
- Auto API discovery & Inventory
- AI runtime protection
- Bot & Abuse defence
- OWASP API Top 10 Aligned
- No SDKs or code changes required.
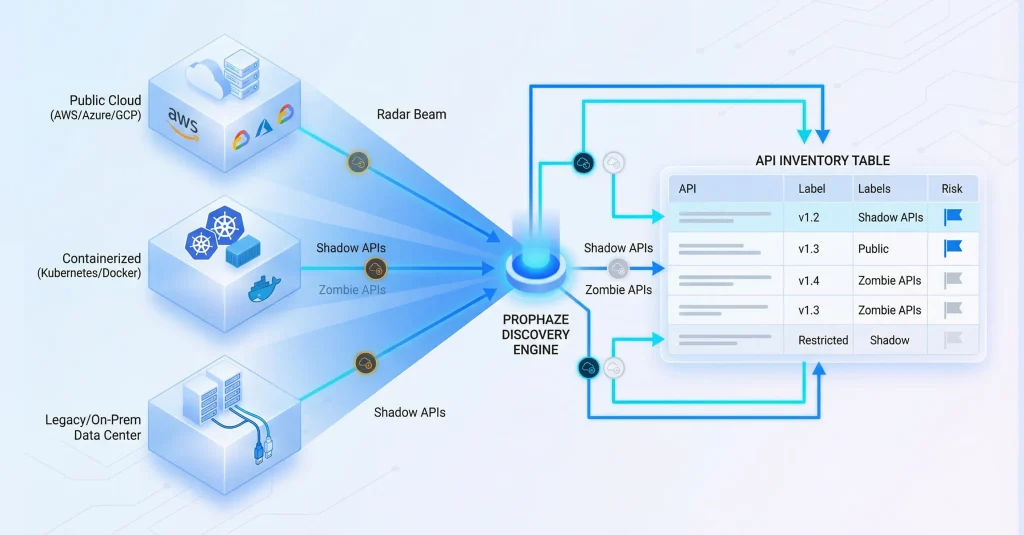
Hidden and Shadow APIs, Prophaze Discovers and Scores the Risk
Before you can secure your APIs, you must know exactly what you have. Prophaze’s discovery engine automatically maps all your APIs, whether documented or not, across internal, external, and partner ecosystems. It delivers a living inventory that updates as your architecture evolves.
Auto discovers APIs across cloud, Kubernetes, containers, and legacy infrastructure.

Monitors schema, versions, and access controls to detect drift and misconfigurations.

Highlights non-compliant or exposed endpoints so your teams know where to act first.
Rising API Threats, Prophaze Delivers Unified Protection
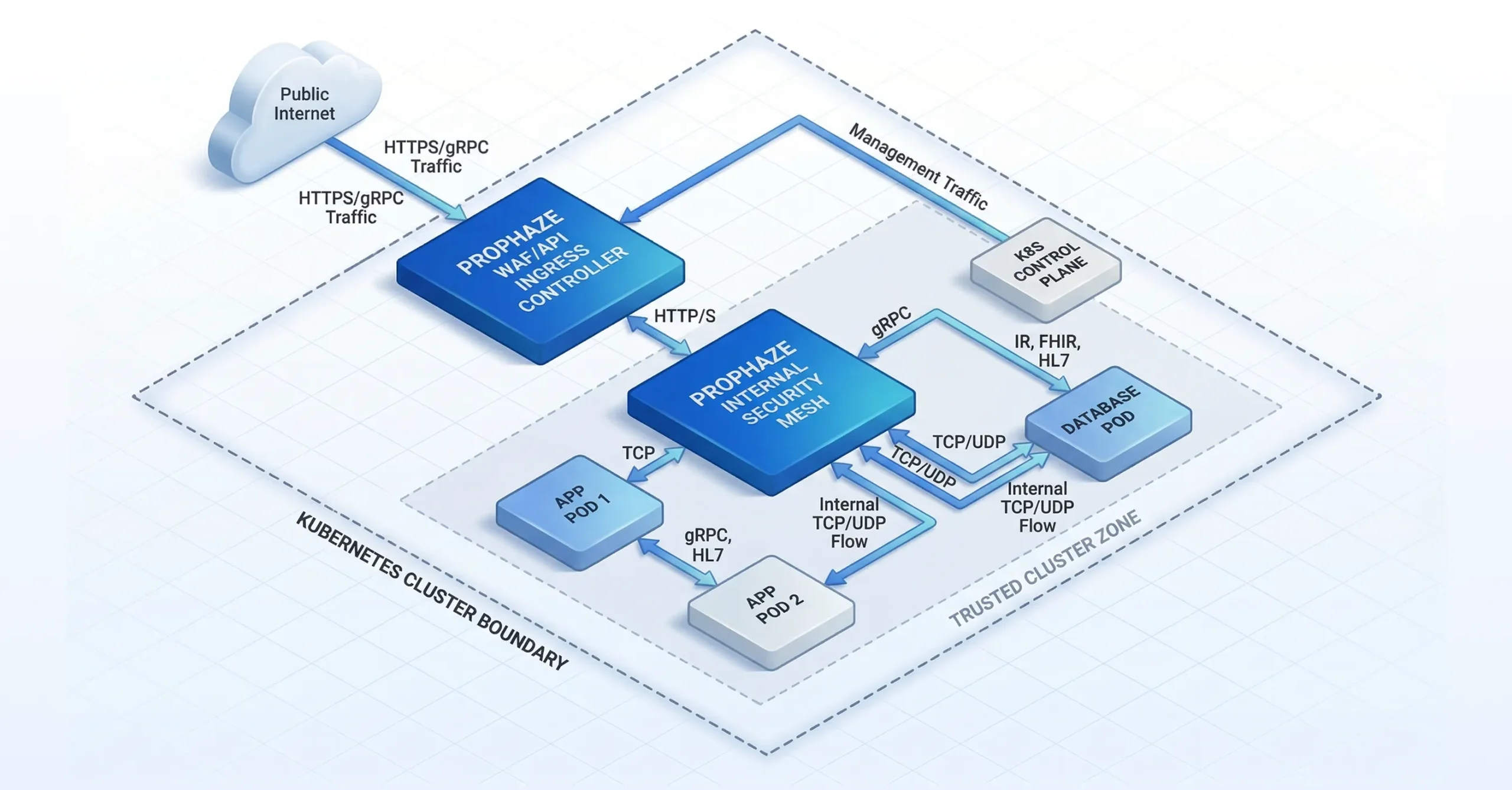
Prophaze combines AI, deep inspection, and Kubernetes-native controls to protect APIs at scale. Security and DevOps teams get powerful defense with minimal operational overhead.

AI-powered threat detection that adapts to new attack patterns in real time.

Bot mitigation at the edge to stop scraping, credential stuffing, and automated abuse.

Zero-day protection that intercepts novel vulnerabilities before they are publicly disclosed.
Schema validation and control for JSON/XML, RBAC, traffic quotas, and granular enforcement.

Shadow API discovery to surface undocumented and legacy endpoints.

Kubernetes-native security for both east-west and north-south traffic.
Compliance-ready policies aligned with PCI-DSS, HIPAA, GDPR, and OWASP standards.
Rising API Threats, Prophaze Delivers Unified Protection
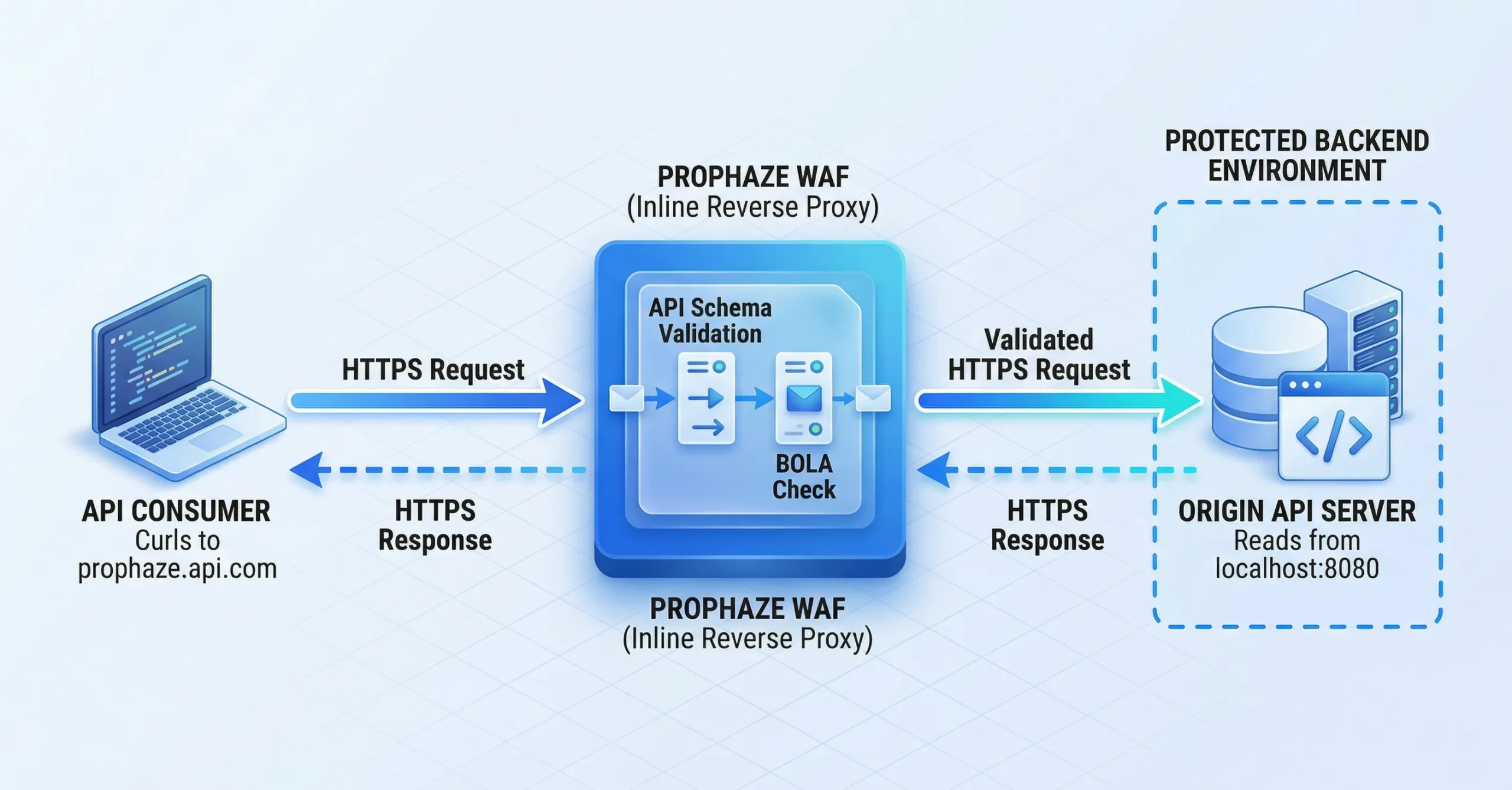
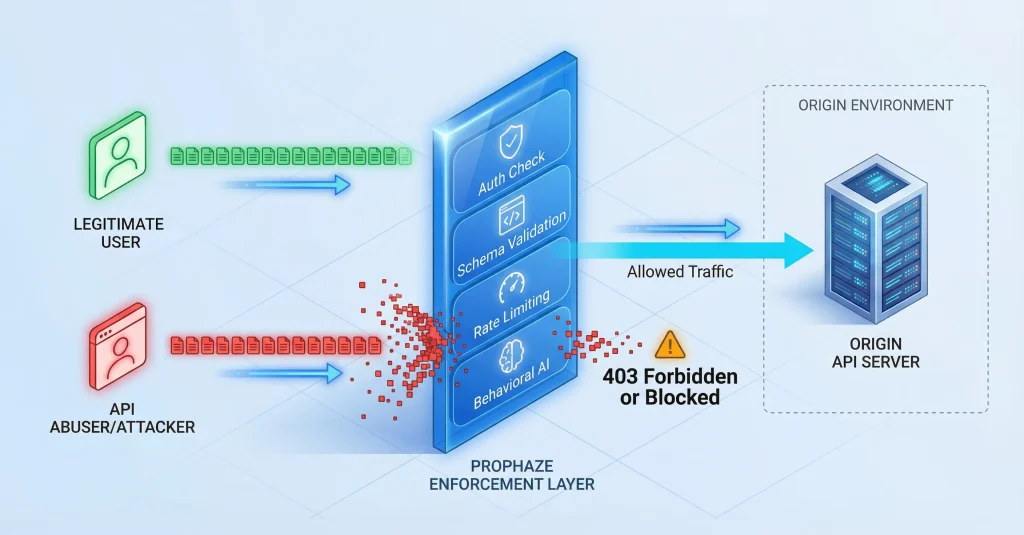
Every API call is analyzed in real time using behavioral analytics, payload inspection, and AI-driven anomaly detection. This enables Prophaze to distinguish legitimate usage from subtle abuse without disrupting normal operations.
Traffic Ingestion
No need for SDKs or code changes. Captures API calls at the edge.
Behavioral Analysis
Analyzes user behavior and evaluates new requests against established baseline patterns.
Real-Time Mitigation
Blocks or challenges suspicious requests without disrupting genuine users.

Prophaze
API Security Cycle
Deep Payload Inspection
Every request and response undergoes a thorough examination to detect any hidden threats.
Anomaly Detection
Instantly, AI flags unusual payloads, data structures, or frequencies.
Continuous Learning
AI models progress in response to emerging traffic patterns and evolving attack vectors.
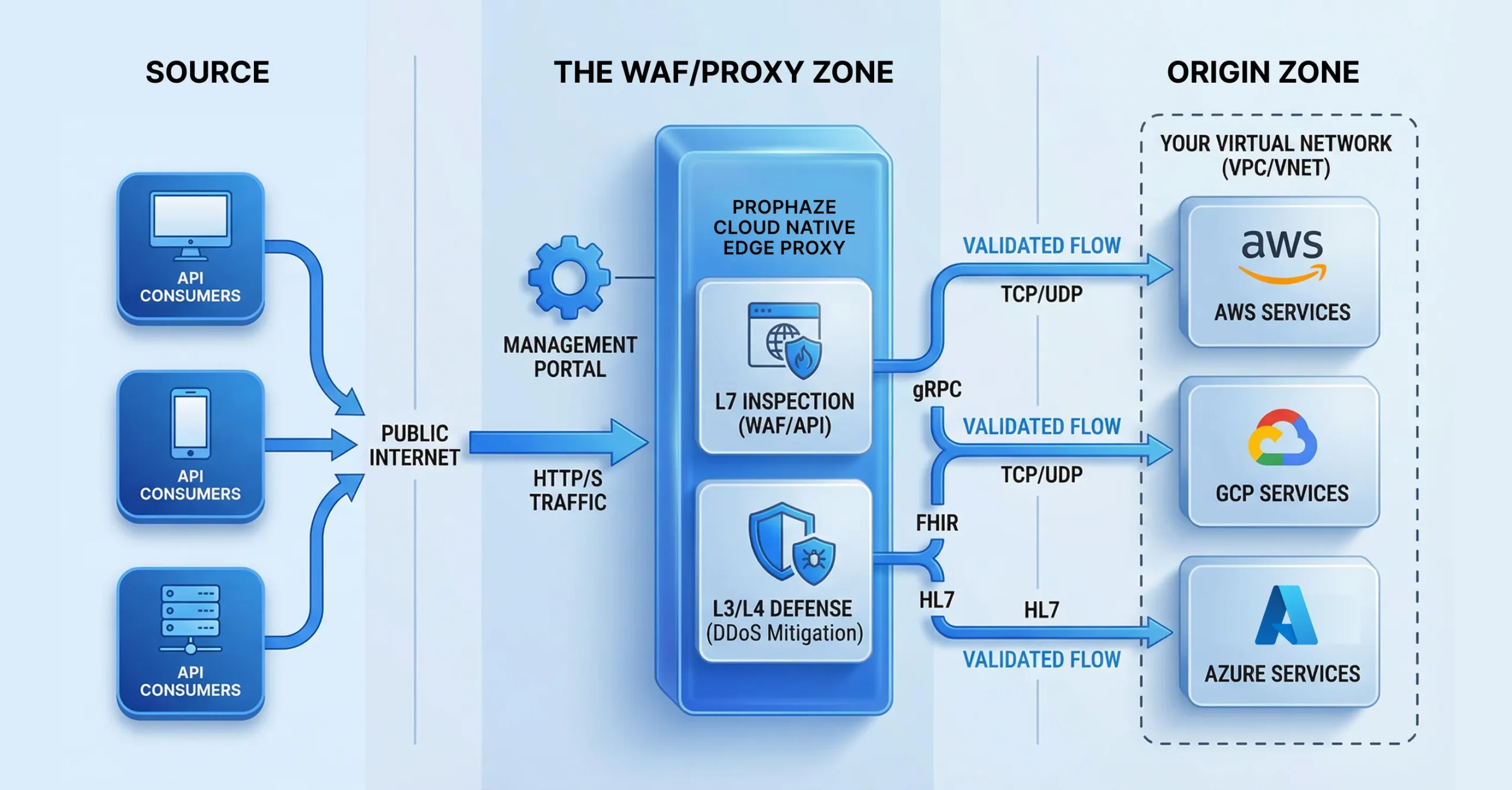
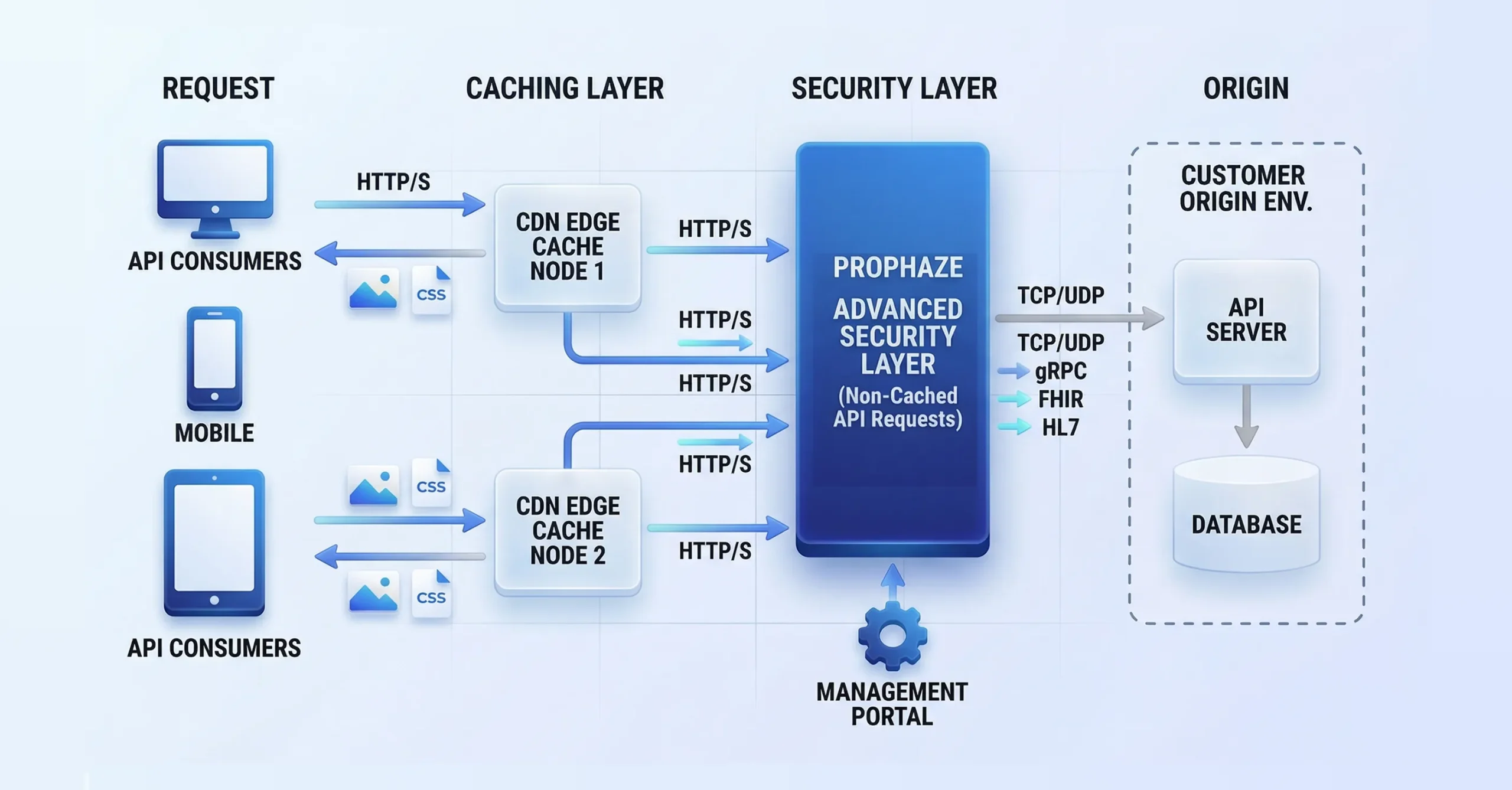
Deployment That Fits, Your Architecture
Prophaze is designed to plug into your environment, not the other way around. You can deploy it in the way that best matches your current infrastructure and growth plans. Flexible models reduce friction for both security and platform teams.
Blind API Sprawl Turned into a Fully Secured Estate in Three Moves
Discover and classify every API
- Auto-discover known, unknown, and shadow APIs across cloud, containers, and legacy environments.
- Continuously track changes to your API inventory, including schema, versions, and access levels.
Assess and prioritize risk
- Classify APIs by sensitivity, exposure, and business criticality.
- Instantly flag high-risk or non-compliant APIs for remediation before they become incidents.

Protect and enforce in real time
- Apply policies for authentication, authorization, schema validation, and rate limits with minimal friction.
- Block abuse, anomalies, and attacks at runtime while keeping legitimate traffic flowing.
- Manufacturing
- Layer 7
Busy DevSecOps Teams, Prophaze Automates API Security in the Pipeline
Prophaze integrates seamlessly into CI/CD pipelines, allowing for security checks throughout development and deployment. It works with RESTful APIs, GraphQL, or gRPC microservices. Prophaze fits your architecture without the need for code rewrites or refactoring.
No SDKs or code rewrites needed

API Security as Code with CI/CD support

Works with REST, gRPC, GraphQL, and OpenAPI specs

Role-based access control (RBAC) and audit trails
Busy DevSecOps Teams, Prophaze Automates API Security in the Pipeline
Security, DevOps, and platform teams share a single, actionable view of API activity. Prophaze’s unified console helps you detect threats faster and enforce policies with confidence. Customizable analytics make it easy to align with your operating model and SLAs.
Visualize every API and service in one pane of glass.
Monitor attack attempts, threat types, and trends in real time.
Trusted by High-Stakes Environments
Prophaze secures APIs for critical infrastructure, global SaaS platforms, healthcare providers, and fintech leaders that cannot afford downtime or data leaks. Security teams rely on Prophaze to reduce risk quickly without adding operational complexity.
Protect Your APIs from Modern Threats
- Secure all API traffic, block abusive bots and zero-day attacks, and get real-time threat insights without slowing delivery.
