
Website Security: Its significance and threats to it!!
Website security refers to the security of organizational and private public-facing websites from various cyber-attacks. These attacks largely impact all

Website security refers to the security of organizational and private public-facing websites from various cyber-attacks. These attacks largely impact all
A vulnerability, which was classified as problematic, was found in XYHCMS 3.6. This affects an unknown part of the file
[vc_row][vc_column][vc_column_text] 5 Facts CISO’s don’t know about WAF #wafwithprophaze [/vc_column_text][/vc_column][/vc_row][vc_row][vc_column][vc_column_text] 39% was the estimate of Web application breaches out
A vulnerability, which was classified as critical, has been found in Booster for WooCommerce Plugin up to 5.4.3 on WordPress
Since COVID-19 has hit the world with its wrath, the business world has turned upside down, companies are shifting to cloud-native
Increments Qiita::Markdown before 0.34.0 allows XSS via a crafted gist link, a different vulnerability than CVE-2021-28796. (CVSS:0.0) (Last Update:2021-06-21)

THIS DOCUMENT IS PROVIDED ON AN “AS IS” BASIS AND DOES NOT IMPLY ANY KIND OF GUARANTEE OR WARRANTY, INCLUDING THE WARRANTIES OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR USE. YOUR USE OF THE INFORMATION ON THE DOCUMENT OR MATERIALS LINKED FROM THE DOCUMENT IS AT YOUR OWN RISK. CISCO RESERVES THE RIGHT TO CHANGE OR UPDATE THIS DOCUMENT AT ANY TIME.A standalone copy or paraphrase of the text of this document that omits the distribution URL is an uncontrolled copy and may lack important information or contain factual errors. The information in this document is intended for end users of Cisco products.

When considering software upgrades, customers are advised to regularly consult the advisories for Cisco products, which are available from the Cisco Security Advisories page, to determine exposure and a complete upgrade solution.
In all cases, customers should ensure that the devices to be upgraded contain sufficient memory and confirm that current hardware and software configurations will continue to be supported properly by the new release. If the information is not clear, customers are advised to contact the Cisco Technical Assistance Center (TAC) or their contracted maintenance providers.
Fixed Releases
At the time of publication, Cisco Small Business RV Series Routers firmware releases 1.0.03.21 and later contained the fix for this vulnerability.
See the Details section in the bug ID(s) at the top of this advisory for the most complete and current information.
To download the firmware from the Software Center on Cisco.com, do the following:
Click Browse all.
Choose Routers > Small Business Routers > Small Business RV Series Routers.
Choose the appropriate router.
Choose Small Business Router Firmware.
Choose a release from the left pane of the product page.
Prophaze SDWAF Your Ultimate Web Application Firewall Solution Prophaze offers advanced Web Application Firewall (WAF) protection that shields your online
NEW DECO IDEAS Decorate For Less With Art Posters & Tasty Accesories Differentiate and you stand out in a very

Safeguarding the company’s assets against existing and emerging vulnerabilities is the most critical task that security teams are struggling with.

Various tools are used to achieve Deep Security virtual patching. It includes: Web Application Firewall (WAF) Intrusion Prevention System (IPS)
From the technical point of view, the initial mitigation strategy would be for an organization to rectify the discovered vulnerability

Today’s systems can be considered as very advanced as well as complex, with multiple dependencies and interrelationships. It requires a
The term patch is misleading because the vulnerable system is not being patched. A quick repair job for a piece
“Virtual Patching” is a term that was initially used by Intrusion Prevention System vendors many years ago. It is also

Kube-Proxy Kube-proxy implements a form of virtual IP for services for all types except ExternalName. Three modes are: (a) Proxy-mode:
CVE-2019-20901 Proof of Concept : The login.jsp resource in Jira before version 8.5.2, and from version 8.6.0 before version
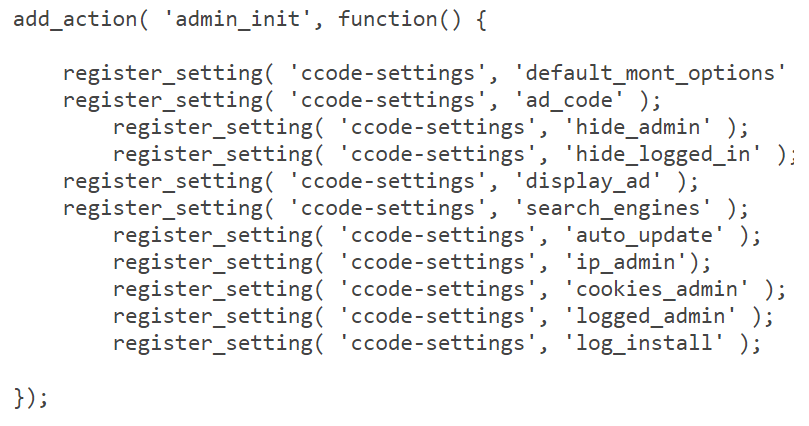
A new variant of popup injector WordPress malware is spreading and affecting 1000s of WordPress websites. The web master was
[vc_row css=”.vc_custom_1595870074355{margin-bottom: -30px !important;}”][vc_column css=”.vc_custom_1595928116608{margin-bottom: 30px !important;}”][vc_column_text] Fixed Price and Unlimited Use Per App Installed on your cloud. No charges for
[vc_row css=”.vc_custom_1592843367172{padding-top: 40px !important;}”][vc_column][vc_column_text]Prophaze Cookie Policy Our website uses cookies to distinguish you from other users of our website. This
[vc_row css=”.vc_custom_1592826839119{padding-top: 0px !important;background-position: 0 0 !important;background-repeat: no-repeat !important;}”][vc_column width=”1/3″][vc_column_text] Zero-Touch Automation Protection from all threats DDoS protection Automated
Overview : NETGEAR R7800 devices before 1.0.2.52 are affected by a stack-based buffer overflow by an authenticated user. Security Advisory
Overview : Certain NETGEAR devices are affected by a stack-based buffer overflow by an authenticated user. This affects D6100 before