Blogs
- Latest Blog
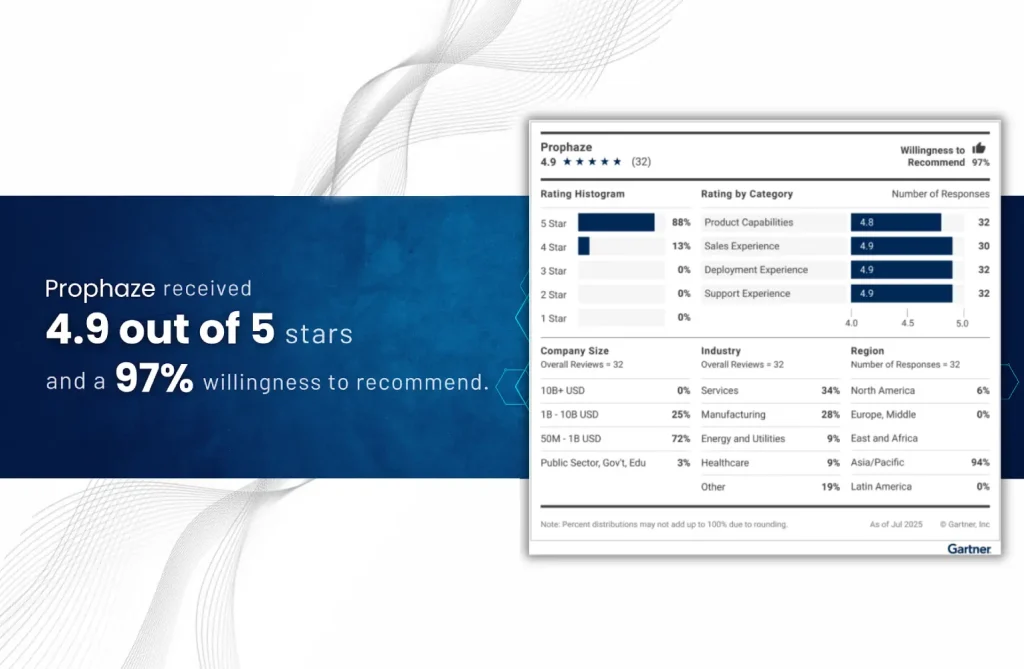
“Voice of the Customer” 2025 for Cloud Web Application and API Protection
- Blog
The Security Gap No Single-Environment WAF Can Close Enterprise hybrid WAF solutions have become essential
- Blog
Why API Disovery Matters in Modern Infrastructure Modern digital infrastructure is mainly driven by APIs
- Blog
Introduction Most modern attacks do not target the network layer. They target web applications, login
- Blog
Introduction Google Cloud Armor secures your infrastructure perimeter. But modern APIs, GKE workloads, and microservices
- Blog
Artificial intelligence is no longer limited to generating responses or summarizing information. Modern AI systems
- Blog
Kubernetes Web Application and API Protection (KWAAP) has become essential as traditional WAFs only secure
- Blog
Is Your Azure Cloud Security Enough? Enterprises running mission-critical workloads on Microsoft Azure are increasingly
- Blog
What Is the DPDP Act of India India’s Digital Personal Data Protection Act (DPDP Act)
- Blog
Understanding Cybersecurity Awareness Month 2025 October marks Cybersecurity Awareness Month (CSAM)—an annual initiative encouraging individuals,
- Blog
A Layer 7 attack—also called an application-layer DDoS attack—is one of the most severe threats
- Blog
In 2025, managed security service providers (MSSPs) are at the center of enterprise defense. With
- Blog
In 2025, Indian enterprises face unprecedented cyber threats — from AI-powered ransomware to shadow API