Your Apps Run Flawlessly, Prophaze SaaS Keeps Them Unbreakable
Stop threats before they hit. Prophaze’s Fully Managed SaaS WAF and API Security platform safeguards your web apps from OWASP Top 10, DDoS floods, bots, and zero-day exploits without servers, scripts, or scaling stress. Get enterprise-grade protection that runs itself, so your team can focus on building, not blocking.
- Fully Managed Security
- Zero Ops overhead
- Always Up-to-date
- Auto-scalling defense
- Unified visibility
Why In-house Security Can’t Keep Up with Modern Application Threats
Security & SOC Teams
Prophaze MashGuard Fix
DevOps / Platform Teams
Prophaze MashGuard Fix

CTOs & Business Leaders
Prophaze MashGuard Fix
From DIY Security Overhead to Effortless, Fully Managed Layer for Web Applications and APIs
Your teams stay focused on innovation, while Prophaze continuously defends against OWASP Top 10 exploits, API abuse, malicious bots, and DDoS attacks without affecting performance or agility.

Step1
Onboard in Minutes - No Infrastructure Required
Step1
Onboard in Minutes - No Infrastructure Required
Step2
Auto‑Protect Every App and API
Step2
Auto‑Protect Every App and API
Step3
Activate Always‑On, Intelligent Defense
Step3
Activate Always‑On, Intelligent DefenseEnable adaptive DDoS mitigation and bot management backed by behavioral AI and global edge presence.
Apply fine-grained controls, including mTLS, geo-fencing, rate limiting, and IP reputation logic, without touching your infrastructure.
Enjoy constant uptime and compliance-ready protection with zero maintenance effort.
Security Outcomes That Grow with Your Applications
Complete elimination of OWASP Top 10 and API Top 10 risks through continuous discovery, AI-adaptive rules, and automated virtual patching across all applications and APIs.
Intelligent bot and scraping defense that distinguishes real users from automation, ensuring seamless user experiences while protecting digital assets and business intelligence.
Unbroken availability during volumetric and multi‑vector DDoS attacks, powered by global edge mitigation that scales instantly with traffic surges.
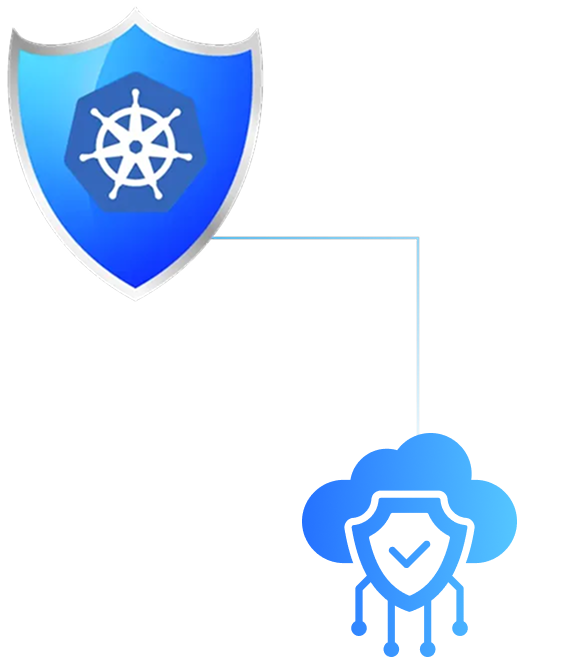
Consistent, unified protection across any environment, cloud, hybrid, or multi‑cloud, without deploying or maintaining hardware, VMs, or gateway appliances.
Centralized visibility and analytics for AppSec, DevOps, and SOC teams with actionable insights, attack forensics, and KPIs that enhance security posture and operational efficiency.
Simplified compliance alignment with PCI‑DSS, SOC 2, ISO 27001, and GDPR via continuous threat reporting, audit-ready dashboards, and automated documentation.
Seamlessly Integrated for Modern Cloud and SaaS Environments





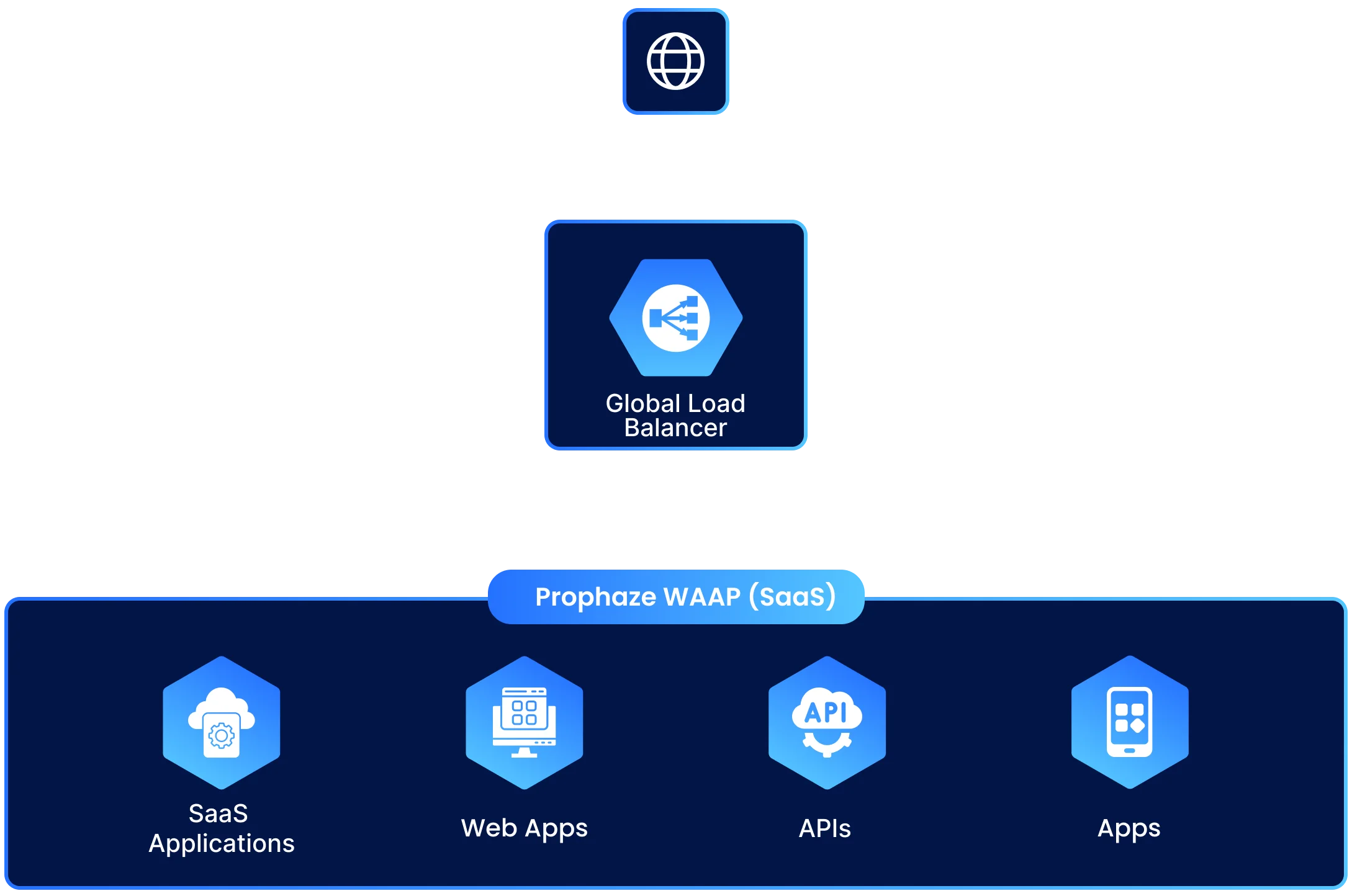
Security That Adapts at SaaS Speed

- Zero deployment friction, with no hardware, VMs, or gateways to maintain, configure, or patch.
- Protection scales instantly with traffic demand across web, mobile, and API workloads.
- Elastic security that adjusts to your architecture in real time, with no lag, no downtime, no reconfigurations.
- Consistent WAAP, WAF, bot, and DDoS protection policies enforced across multiple business apps and teams.

- 24×7 monitoring and real-time analytics with AI-driven anomaly detection across all attack surfaces.
- Unified dashboards with actionable insights for threat response, posture assessment, and compliance validation.
- Behavioral machine learning reduces false positives, so you catch true threats, not noise.
- Continuous virtual patching against OWASP, API Top 10, and zero-day variants without developer intervention.

- Policy-as-code integrations enable version-controlled security across environments.
- Works seamlessly with CI/CD tools (GitHub Actions, Jenkins, GitLab CI, Azure DevOps) for automated testing and safe deploys.
- Instant rollout of new protections—validated in your pipeline before production.
- Security shifts left without slowing release velocity or engineering productivity.
Unified Security Intelligence Across All Applications & API

Understand traffic in real time, who’s accessing which apps and APIs, from where, and using what patterns, across all environments and regions.

Detect anomalies and attacks instantly through AI‑driven baselines that differentiate legitimate user behavior from automated threats or API abuse.

Accelerate investigation and response with full context, including request payloads, rule triggers, API endpoints, and correlated event histories.

Share unified insights across SOC, DevOps, and compliance teams with exportable reports and dashboards.

Integrate seamlessly with your existing stack for continuous visibility and incident automation.
Integrations
Cloud-Native WAAP Capabilities Legacy WAFs Can’t Match
Threat Protection
- Comprehensive coverage for OWASP Web & API Top 10 risks—including SQLi, XSS, RCE, credential stuffing, and business logic abuse across any environment.
- API‑centric defense with schema validation, sensitive data inspection, adaptive rate limiting, and automated virtual patching for exposed or shadow APIs.
- Always‑on L3–L7 protection powered by AI and behavioral analytics—stopping bots, scraping, credential abuse, and complex multi‑vector DDoS attacks before they hit your apps.
- Self‑tuning security engine that continuously adapts policies to traffic context—ensuring precise detections without blocking legitimate users.

Operations & Governance
- Centralized policy orchestration for web, API, bot, and DDoS protections across all applications, teams, and geographies—managed entirely within the Prophaze SaaS console.
- Role‑based visibility & audit trails with SSO, granular permissions, and version‑controlled configurations for accountability and compliance.
- Environment‑aware segmentation that isolates dev, staging, and production zones—allowing safe testing, policy promotion, and rollback automation.
- Compliance‑ready visibility with continuous monitoring, reporting, and exportable logs for PCI‑DSS, SOC 2, GDPR, and ISO 27001 audits.

Automation & Integration
- No deployment overhead—instant integration via DNS or connector, activating protection for web apps and APIs in minutes.
- CI/CD & DevSecOps‑friendly APIs for dynamic policy enforcement and version control alongside infrastructure or app code.
- Automatic learning and rule propagation across all endpoints—no manual updates, no drift.
- Seamless visibility integrations with Splunk, Datadog, Elastic, Microsoft Sentinel, and ServiceNow for unified security analytics and response workflows.
- Dry‑run & simulation modes to test policy changes and threshold tuning safely before enforcement.

Proven Enterprise-Ready WAAP for Modern SaaS and Cloud Workloads






















