What is Serialization?
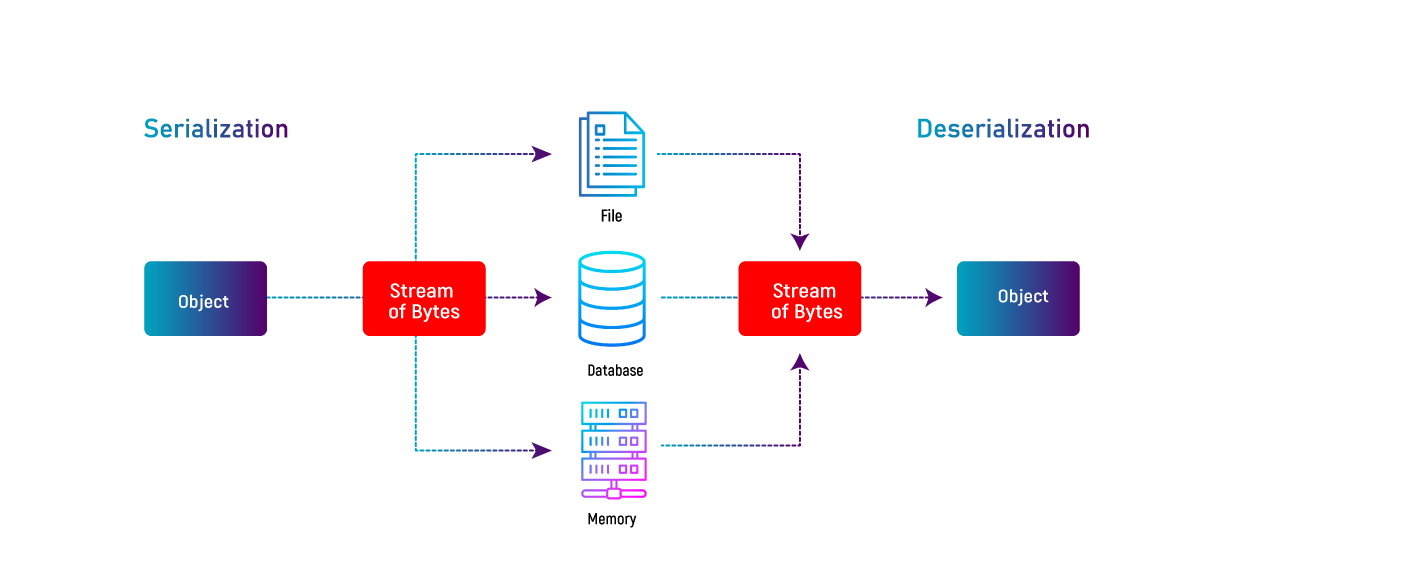
Serialization is the process of turning an item into a format that can be transmitted over a network, sent through streams (such as stdout), or persisted to disc (such as stored to a file or datastore).
There are many different serialization formats, including JSON, XML, YAML, Protocol Buffers, and MessagePack. Each format has its own strengths and weaknesses, and the choice of serialization format depends on the specific requirements of the application or system.
JSON and XML are two of the most commonly used serialization formats within web applications.
What is Deserialization?
Deserialization on the other hand, is the inverse process, where the serialized data is read and converted back into its original form.
This process is often used in distributed systems and network communication, where data needs to be transmitted between different processes or machines.
One of the challenges of deserialization is ensuring that the serialized data is safe and secure. Malicious actors may attempt to inject code or other harmful payloads into the serialized data, which could be executed during the deserialization process. To prevent this, it is important to use secure deserialization libraries and to carefully validate the input data before deserializing it.
What is Insecure Deserialization?
Insecure deserialization is a security vulnerability that arises when an application fails to properly validate or sanitize serialized data.
Insecure deserialization can lead to a wide range of attacks, including remote code execution, injection attacks, and denial-of-service attacks.
One of the main reasons insecure deserialization is so dangerous is because it can often bypass traditional security measures, such as input validation and sanitization.
To better understand the risks of insecure deserialization, let’s look at a few common attacks. Let’s examine a few typical attack scenarios in order to better comprehend the dangers of unsecured deserialization:
Remote Code Execution (RCE):
In an RCE attack, a serialised payload containing executable code is sent by the attacker. The programme unintentionally runs the code when it deserializes the data, giving the attacker total control of the system. This type of attack can be particularly dangerous because it can often bypass firewalls and other security measures that are designed to prevent code execution.
Injection Attacks:
In an injection attack, an attacker sends a serialized payload that contains data that is injected into the application’s code. This can include SQL injection, LDAP injection, and other types of injection attacks. When the application deserializes the data, it unwittingly incorporates the injected code into its own operations, potentially exposing sensitive information or compromising the system.
Denial-of-Service (DoS) Attacks:
In a DoS attack, an attacker sends a serialized payload that causes the application to consume excessive resources, such as CPU time or memory. This can cause the application to become unresponsive or even crash, effectively denying service to legitimate users.
How to protect the application from Insecure Deserialization Attacks?
The first step is to ensure that the application properly validates and sanitizes all incoming data, including serialized data. This can involve implementing input validation routines that check the format, length, and content of serialized data, as well as implementing secure deserialization libraries that are designed to prevent known vulnerabilities.
In addition, we could also implement other security measures, such as rate limiting and network segmentation, to limit the impact of any potential attacks. Regular security audits and penetration testing can also help to identify and remediate vulnerabilities before they can be exploited by attackers.
Conclusion
Insecure deserialization is a serious security risk that can lead to a wide range of attacks. By understanding the risks and taking steps to protect the application, you can help to prevent these types of attacks and keep your system secure.