Critical authentication bypass vulnerability found in Alfresco Community Edition (CVE-2019-14222)
An issue was discovered in Alfresco Community Edition versions 6.0 and lower. An unauthenticated, remote attacker could authenticate to Alfresco’s Solr Web Admin Interface. The vulnerability is due to the presence of a default private key that is present in all default installations. An attacker could exploit this vulnerability by using the extracted private key and bundling it into a PKCS12. A successful exploit could allow the attacker to gain information about the target system (e.g., OS type, system file locations, Java version, Solr version, etc.) as well as the ability to launch further attacks by leveraging the access to Alfresco’s Solr Web Admin Interface.
CVE-2019-14222: Alfresco Default Certificate
Alfresco Community instalations, versions 6.0 and lower, come installed with static SSL certificates.
These certificates are used in 2 ways:
-
Authenticating to the Solr Admin Web Interface
-
Encrypting Client-Server traffic
Authenticating to the Solr Admin Web Interface
The browser.p12, with password “alfresco”, file can be installed in a browser in order to authenticate via X509 Mutual Authentication Protocol.
Note: As and alternative, if the public certificates have been modified, but the private key was kept the same, one can use the alfresco.rsa private key in burp in order to forcefully authenticate using this private key.
STEPS:
-
Import browser.p12, with password “alfresco”, in your browser of choice (In this case Firefox).
-
Navigate to URL “
/solr4/” of a victim with Alfresco Community installed. -
Use the imported certificate to authenticate to Solr.
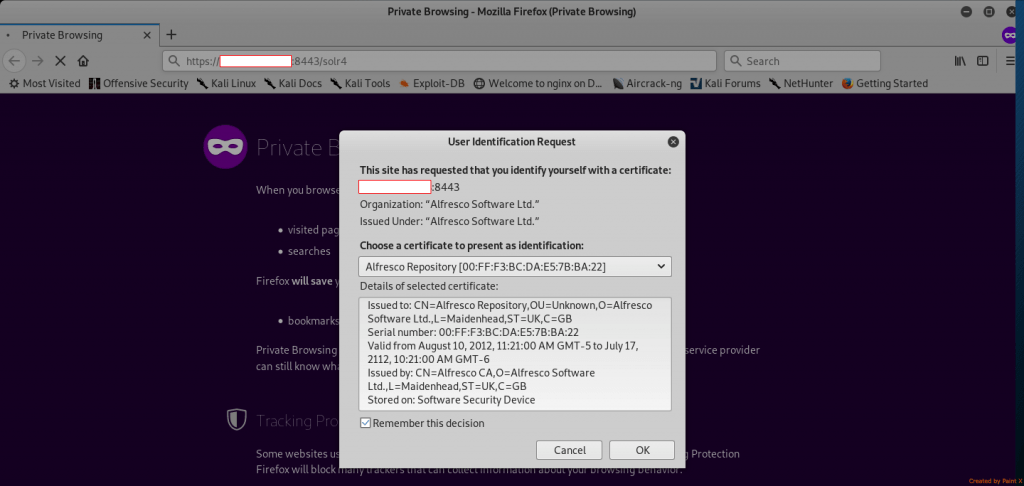
-
Get access to Alfresco’s Solr Web Admin Interface.
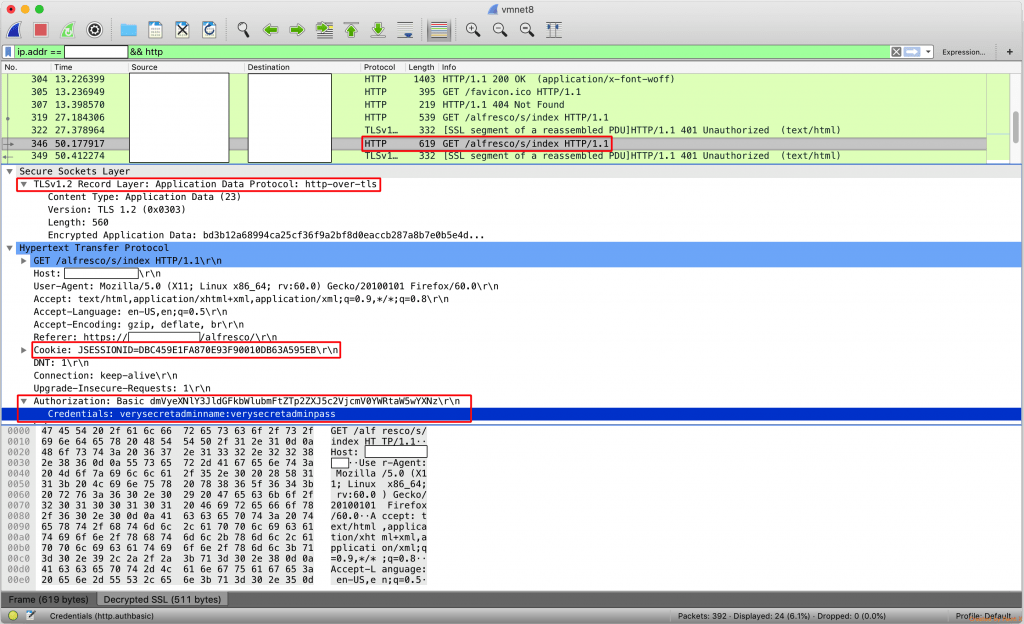
Decrypting Client-Server traffic
By knowing the private key used by Alfresco to encrypt HTTP traffic, alfresco.rsa, an attacker may leverege it to launch:
-
Active Man-in-the-Middle Attacks using a valid certificate.
-
Passive Decrytion (if non-Perfect Forwarding Secrecy (PFS) encryption ciphers are used).
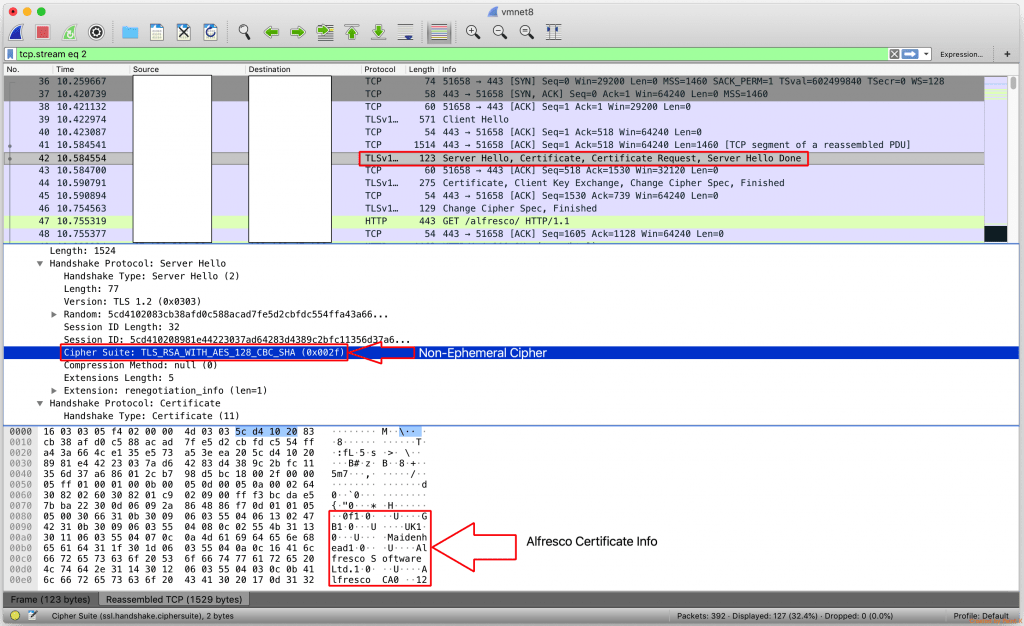
Example Passive Decryption
-
Capture/Obtain Client-Server traffic.
-
Decrypt the traffic using the alfresco.rsa private key.