
Deploying Prophaze WAF On-Premises On GCP
Prophaze WAF is a security tool that can secure your web applications from various attacks. It can be deployed on

Prophaze WAF is a security tool that can secure your web applications from various attacks. It can be deployed on
API Security API Security for Your Data Privacy Prophaze API Security is a comprehensive solution to secure APIs from various

Protect Your on-premises AWS Workloads with Prophaze WAF Deploying Prophaze WAF on your on-premises AWS workloads allows you to have
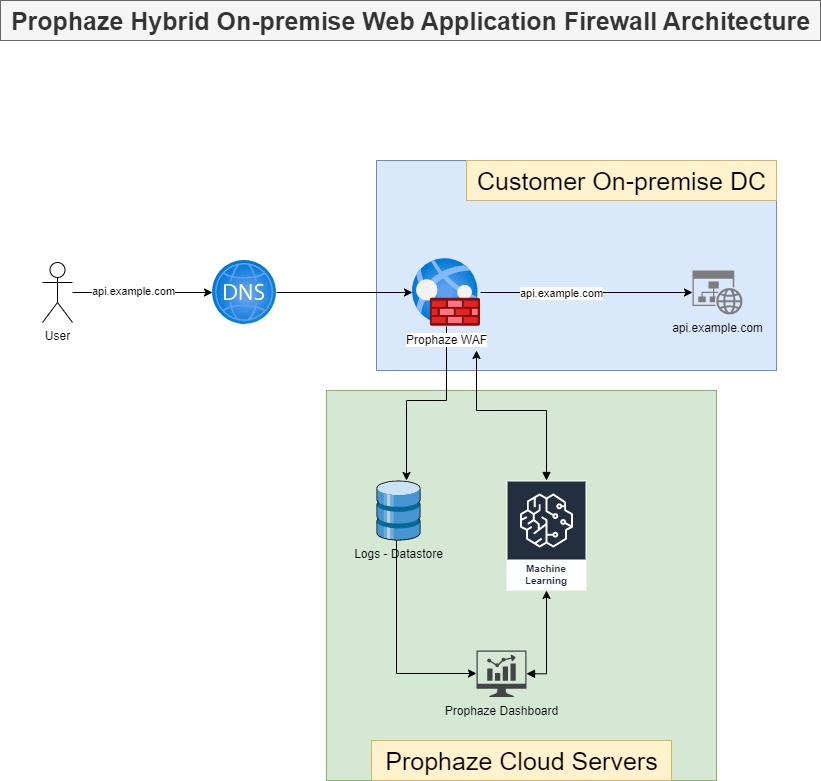
On-Premises WAF Prophaze WAF Supports On-Premises Prophaze WAF support on-premises deployment to ensure compliance with security in industries such as
Prophaze WAF 3.0 Secure, Simpler, and Safer Prophaze WAF 3.0 is a Distributed proactive web security platform designed to defend
Zero-Configuration Web Application and API Protection for Kubernetes Zero-Configuration Web Application and API Protection (WAAP), DDoS protection and Bot Mitigation

Description Affected versions of Atlassian Jira Server and Data Center allow anonymous remote attackers to inject arbitrary HTML or JavaScript
Description A stored cross-site scripting (XSS) vulnerability in Mealie v0.5.5 allows attackers to execute arbitrary web scripts or HTML via

Description Cross Site Scripting (XSS) vulnerability in Joplin Desktop App before 1.8.5 allows attackers to execute aribrary code due to

Description A cross-site scripting (XSS) vulnerability in the SEOmatic plugin 3.4.10 for Craft CMS 3 allows remote attackers to inject

The OWASP Top 10 API security is a classification of the most common attacks on the web. The vulnerabilities exploited

Cross-site scripting (XSS) vulnerability in the Asset module’s edit vocabulary page in Liferay Portal 7.0.0 through 7.3.4, and Liferay DXP

Cross Site Scripting (XSS) vulnerability in Roundcube Mail <=1.4.4 via smtp config in /installer/test.php. (CVSS:0.0) (Last Update:2021-06-24)

Shopware is an open source eCommerce platform. Versions prior to 5.6.10 suffer from an authenticated stored XSS in administration vulnerability.
Cross Site Scripting (XSS) vulnerability in MetInfo 7.0.0 via the gourl parameter in login.php. (CVSS:0.0) (Last Update:2021-06-21)
Increments Qiita::Markdown before 0.34.0 allows XSS via a crafted gist link, a different vulnerability than CVE-2021-28796. (CVSS:0.0) (Last Update:2021-06-21)
Jenkins Scriptler Plugin 3.1 and earlier does not escape script content, resulting in a stored cross-site scripting (XSS) vulnerability exploitable
Jenkins Scriptler Plugin 3.2 and earlier does not escape parameter names shown in job configuration forms, resulting in a stored

The vulnerabilities are dependent on one another; exploitation of one of the vulnerabilities is required to exploit the other vulnerability.
Details about the vulnerabilities are as follows:
Cisco Finesse and Cisco Virtualized Voice Browser OpenSocial Gadget Editor Unauthenticated Access Vulnerability
A vulnerability in the web management interface of Cisco Finesse and Cisco Virtualized Voice Browser could allow an unauthenticated, remote attacker to access the OpenSocial Gadget Editor without providing valid user credentials.
The vulnerability is due to missing authentication for a specific section of the web-based management interface. An attacker could exploit this vulnerability by accessing a crafted URL. A successful exploit could allow the attacker to obtain access to a section of the interface, which they could use to obtain potentially confidential information and create arbitrary XML files.
Cisco has released software updates that address this vulnerability. There are no workarounds that address this vulnerability.
CVE ID: CVE-2021-1246Bug ID(s): CSCvs52916, CSCvw27957Security Impact Rating (SIR): MediumCVSS Base Score: 6.5CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:N
Cisco Finesse OpenSocial Gadget Editor Cross-Site Scripting Vulnerability
A vulnerability in the web-based management interface of Cisco Finesse could allow an unauthenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the interface.
The vulnerability exists because the web-based management interface does not properly validate user-supplied input. An attacker could exploit this vulnerability by persuading a user of the interface to click a crafted link. A successful exploit could allow the attacker to execute arbitrary script code in the context of the interface or access sensitive, browser-based information.
Cisco has released software updates that address this vulnerability. There are no workarounds that address this vulnerability.
CVE ID: CVE-2021-1245Bug ID(s): CSCvs52916Security Impact Rating (SIR): MediumCVSS Base Score: 6.1CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
Jenkins Kiuwan Plugin 1.6.0 and earlier does not escape query parameters in an error message for a form validation endpoint,
A reflected Cross-Site Scripting (XSS) flaw was found in RESTEasy in all versions of RESTEasy up to 4.6.0.Final, where it
SAP NetWeaver Application Server ABAP (Applications based on SAP GUI for HTML), versions – KRNL64NUC – 7.49, KRNL64UC – 7.49,7.53,
Prophaze WAF Role Security Reliable, Automated Blocking Prophaze WAF 3.0 is a Distributed proactive web security platform designed to defend