CVE-2023-28116 : CONTIKI-NG UP TO 4.8/4.9 BLE L2CAP MODULE PACKETBUF_SIZE BUFFER OVERFLOW
Description Contiki-NG is an open-source, cross-platform operating system for internet of things (IoT) devices. In versions 4.8 and prior, an
Description Contiki-NG is an open-source, cross-platform operating system for internet of things (IoT) devices. In versions 4.8 and prior, an

What is SQL Injection? SQL injection is a type of cyber attack that targets web applications that use Structured Query
Prophaze offers a wide range of cybersecurity solutions, including securing third-party API integrations. Helps to identify and mitigate potential security
Description In PHP 8.0.X before 8.0.28, 8.1.X before 8.1.16 and 8.2.X before 8.2.3, password_verify() function may accept some invalid Blowfish
Advantages of Prophaze WAF As A Service Customer Retention with WAF as a Service WAF configuration is tricky and with
Description A backdoor in Solar-Log Gateway products allows remote access via web panel gaining super administration privileges to the attacker.
Description Sofia-SIP is an open-source SIP User-Agent library, compliant with the IETF RFC3261 specification. In affected versions Sofia-SIP **lacks both

Web Application Firewalls (WAF) have existed for quite some time to safeguard web applications by inspecting HTTP traffic. Traditionally, on-premises WAFs
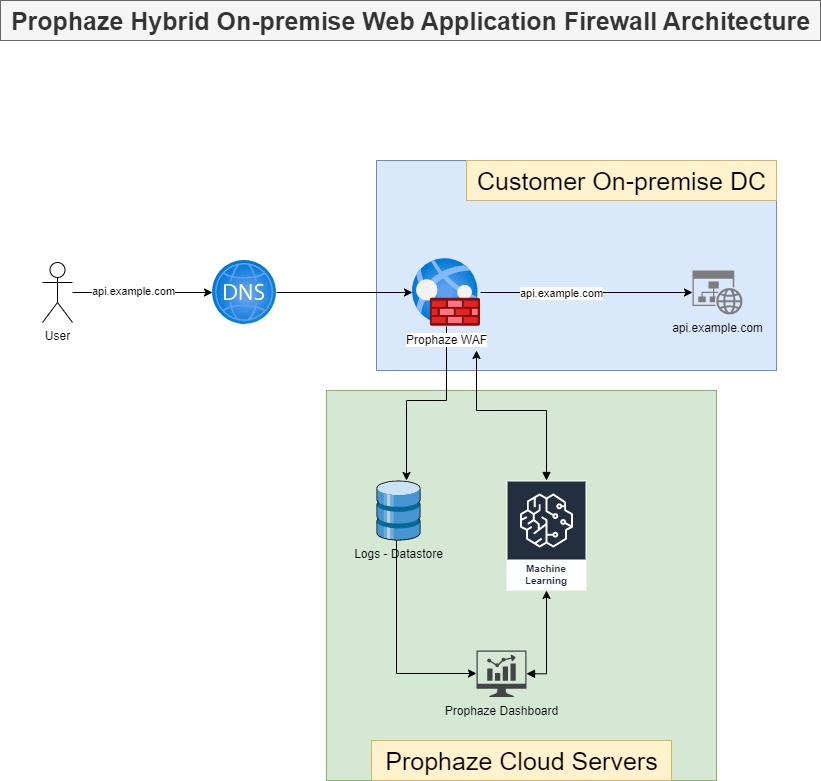
On-Premises WAF Prophaze WAF Supports On-Premises Prophaze WAF support on-premises deployment to ensure compliance with security in industries such as

Description authentik is an open-source Identity Provider focused on flexibility and versatility. Versions prior to 2022.11.4 and 2022.10.4 are vulnerable

The conventional Model is WAF 1.0 Hardware-driven, not scalable, typically rule-based architecture which came into existence in the early 2000s.
Prophaze WAF 3.0 Secure, Simpler, and Safer Prophaze WAF 3.0 is a Distributed proactive web security platform designed to defend

Prophaze Helps the Healthcare Industry from ransomware attacks Such a company facing this kind of attacks deployed Prophaze, and it
Description Pimcore is an open source data and experience management platform. Prior to version 10.5.9, the user controlled twig templates
Description A vulnerability regarding improper restriction of operations within the bounds of a memory buffer is found in the message
What is SSL? SSL stands for Secure Sockets Layer. It is a standard technology for establishing an encrypted link between

What is Directory Traversal? Directory traversal is also known as file path traversal. It is a web security flaw that
What Is Credential Stuffing? A cyberattack known as “credential stuffing” occurs when a cybercriminal gains access to user accounts at
Description isolated-vm is a library for nodejs which gives the user access to v8’s Isolate interface. In versions 4.3.6 and
What is Remote File Inclusion (RFI)? RFI is also known as Remote file inclusion. In this the attackers or Penetration

What is Session Hijacking? Session Hijacking is the type of attack in which the attacker takes over or hijacks a

What is a Supply Chain Attack? The supply chain includes everything from the delivery of materials from suppliers to manufacturers
What Is Clickjacking? Users are tricked into believing they are clicking on one thing when they are actually clicking on
What Is Remote Code Execution? Remote Code Execution or RCE, also known as arbitrary code execution is a network vulnerability